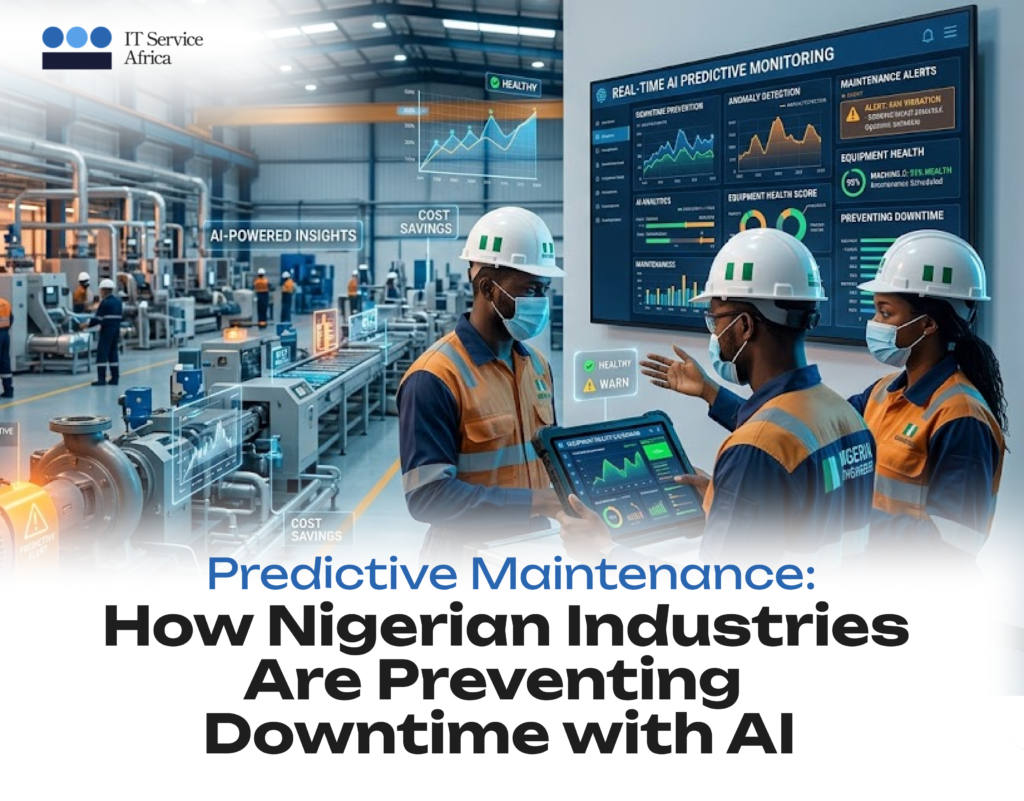
Equipment failure is expensive anywhere. In Nigeria, where supply chains are long, technical expertise is scarce, and margins are tight, unplanned downtime can be catastrophic. A single generator failure during peak production, a conveyor breakdown at a critical moment, or a pump failure at an industrial site creates costs far beyond the repair bill. AssetNova changes this equation. By predicting failures before they happen, this AI-powered platform helps Nigerian organizations shift from reactive firefighting to proactive control thereby transforming maintenance from cost center to competitive advantage. The Maintenance Challenge in Nigerian Industry Nigeria’s industrial sector faces distinctive pressures: Traditional maintenance approaches either “run until it breaks” or rigid scheduled maintenance all fail to address these realities efficiently. The True Cost of Equipment Failure When critical assets fail unexpectedly, Nigerian businesses pay multiple prices: Immediate Production Losses Every hour of stopped production is revenue lost forever. For a manufacturing line generating ₦10 million daily, a two-day outage costs ₦20 million in lost output alone. Emergency Repair Premiums Rush shipping for parts, overtime labor, and expedited service contracts multiply normal maintenance costs by 3-5x or more. Secondary Damage Initial failures often cascade damaging connected equipment, contaminating production batches, or creating safety incidents. Customer and Contract Penalties Missed delivery deadlines, broken service agreements, and damaged relationships create lasting business consequences. Regulatory and Safety Risks Equipment failures in regulated industries create compliance violations and potential liability exposure. How AssetNova Predicts and Prevents Failure AssetNova applies machine learning to equipment data transforming maintenance from calendar-based guesswork to condition-based precision: Continuous Monitoring Sensors track vibration, temperature, pressure, electrical current, and other indicators of equipment health. Data flows from SCADA systems, PLCs, IoT devices, and historians into a unified analytics platform. Pattern Recognition AI models learn normal operating patterns for each asset and then detect subtle deviations indicating developing problems. These patterns are invisible to human observation but obvious to machine intelligence. Failure Prediction Rather than vague “something might be wrong” alerts, AssetNova provides specific failure predictions with confidence intervals and time horizons—”Bearing failure likely in 14-21 days” rather than “Check bearing.” Prescriptive Action The platform automatically generates work orders, schedules maintenance crews, orders required parts, and optimizes maintenance timing to minimize production impact. Continuous Learning As more data accumulates, prediction accuracy improves. AssetNova achieves 94%+ prediction accuracy in typical deployments, with 30-40% total maintenance cost reduction. Designed for Nigerian Industrial Realities AssetNova addresses specific challenges Nigerian organizations face: Air-Gapped and Hybrid Deployment For security-sensitive operations in energy, defense, and critical infrastructure, AssetNova deploys in isolated environments without external connectivity maintaining security while delivering intelligence. Integration with Existing Infrastructure The platform connects with existing SCADA systems, historians, and control systems without requiring wholesale infrastructure replacement protecting capital investment. Support for Critical Industries Rapid ROI Typical implementations show return on investment within 6-8 weeks through prevented failures and optimized maintenance scheduling. The Transformation Journey Implementing predictive maintenance follows a structured path: Assessment Review current maintenance practices, identify critical assets, and evaluate data availability. Data Integration Connect relevant data sources—SCADA, IoT sensors, maintenance records, operational parameters. Model Training AI models learn equipment-specific patterns using historical data, refined through expert input. Pilot Validation Test predictions against actual outcomes, refine thresholds, and build organizational confidence. Scale and Optimize Expand to additional assets, integrate with maintenance management systems, and continuously improve. Building Resilient Operations For Nigerian industries, AssetNova enables: Conclusion AssetNova provides the predictive intelligence organizations need to transform maintenance from reactive cost to proactive advantage. For Nigerian manufacturers, energy operators, miners, and critical infrastructure providers, AI-powered predictive maintenance is no longer futuristic technology. It is available, proven, and essential for sustainable operations.