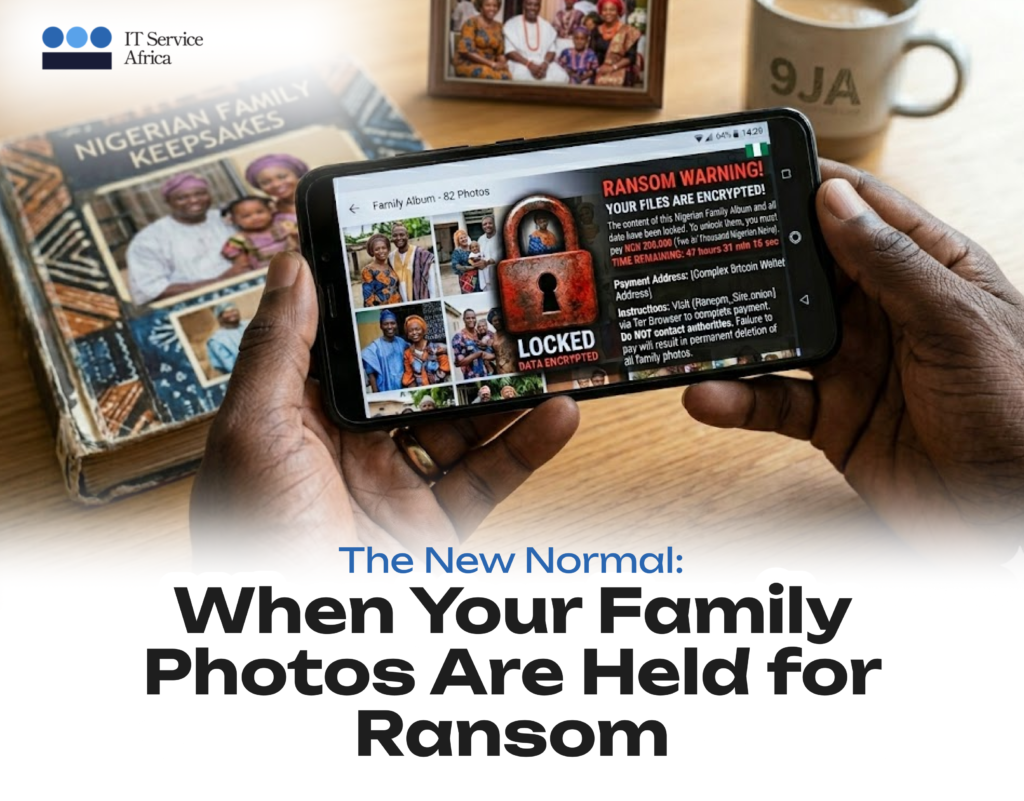
Last Tuesday, a Lagos-based accountant clicked an email that looked like her bank’s security alert. By Wednesday, her laptop’s screen displayed a simple message: ‘Your files are encrypted. Pay $2,000 in Bitcoin or lose everything.’
Her wedding photos, her children’s school records, five years of client tax documents all gone or held hostage, which felt worse.
While this is a representative scenario rather than a single reported event, it mirrors the reality of a growing wave of ‘double extortion’ ransomware attacks currently targeting professionals across Nigeria.
She paid. Most people do. The FBI says 41% of ransomware victims pay, and the average demand now exceeds $1.5 million for businesses. For individuals, the numbers are smaller but the desperation identical.
This is the new normal and it’s arriving in Nigerian living rooms faster than anyone prepared for.
The Global Shift
Cybercrime is now the world’s third-largest economy, behind only the US and China. Estimated annual damage: $8 trillion.
That’s not a typo… Trillions.
What changed? Three things converged.
First, remote work dissolved the perimeter. Your home network is now your office network. Your child’s tablet shares bandwidth with your banking session. The castle walls disappeared.
Second, AI lowered the skill floor. Attackers no longer need coding expertise. Generative AI writes convincing phishing emails in any language, tailored to any target. The Nigerian prince scam evolved into something far more sophisticated.
Third, cryptocurrency made payment untraceable. Ransom demands became practical. Before Bitcoin, kidnapping data made no sense. Now it makes billions.
The Nigerian Context
Nigeria’s digital adoption curve is steep and recent. Mobile banking exploded. SME e-commerce emerged overnight. Government services moved online. The convenience was immediate. The security awareness lagged by years.
Consider the typical Nigerian household now:
- Four smartphones on one WiFi network
- Mobile banking apps with biometric login
- Children’s school portals storing personal data
- Smart TVs, security cameras, voice assistants—all connected, rarely updated
- Shared passwords because “it’s easier”
Each device is an entry point. Each convenience is a vulnerability and the attackers know Nigeria’s growing middle class represents fresh targets with limited preparation.
Why Families Specifically
Businesses receive cybersecurity attention; families rarely do. Yet, the emotional damage is often greater.
A compromised family email account becomes a platform for identity theft. Stolen children’s photos appear in extortion schemes, and compromised banking credentials drain savings built over years. The violation feels personal because it is.
The psychological toll exceeds financial loss. Victims report anxiety, shame, and a persistent distrust of digital tools that society now requires them to use. The “just don’t click suspicious links” advice sounds hollow after the fact.
What Actually Works
Awareness helps but isn’t sufficient. Individual vigilance cannot compensate for systemic vulnerability; effective protection requires a layered defense:
- Email filtering that catches malicious messages before human judgment is tested.
- Endpoint protection on every device, not just work laptops.
- Network security that segments home traffic; your banking shouldn’t share space with your smart fridge.
- Regular backups that render ransomware toothless. Encrypted files matter less when clean copies exist.
- Training that evolves as attacks do. Yesterday’s red flags differ from tomorrow’s.
The ITSA Approach
Our cybersecurity services aren’t designed for abstract enterprises. They’re built for normal apartments and family homes as much as corporate headquarters.
We implement:
- ISO 27001-certified frameworks adapted to Nigerian operational realities
- Email and web filtering that protects every connected device
- Endpoint detection that isolates threats before spread
- Backup systems that actually restore when needed
- Training that respects intelligence without assuming technical expertise
For families, this means protection that doesn’t require technical sophistication to maintain. For businesses, it means security that scales without becoming another management burden.
The Sovereignty Question
Global cybersecurity solutions often assume reliable power, consistent connectivity, and Western regulatory frameworks. Nigeria’s reality differs. Effective protection here must function despite infrastructure gaps, accommodate mobile-first usage patterns, and respect data sovereignty concerns.
Generic solutions fail. Contextual adaptation succeeds.
Moving Forward
The question is no longer, whether Nigerian families and businesses will face cyber threats. They already do, often unknowingly. The question is whether preparation precedes crisis.
For the accountant who paid $2,000, the lesson was expensive. For others, it need not be.
Technology should connect without exposing. Convenience should not require vulnerability.
In addition, security should be accessible without requiring a computer science degree.
ITSA applies that standard to every client, every family and every connected device.

Leave a Comment